Intro to Webhooks
How to Automate Tasks with HTTP Callbacks
A complete guide to real-time event-driven architecture, API efficiency, and the engineering reality of securing distributed payloads.
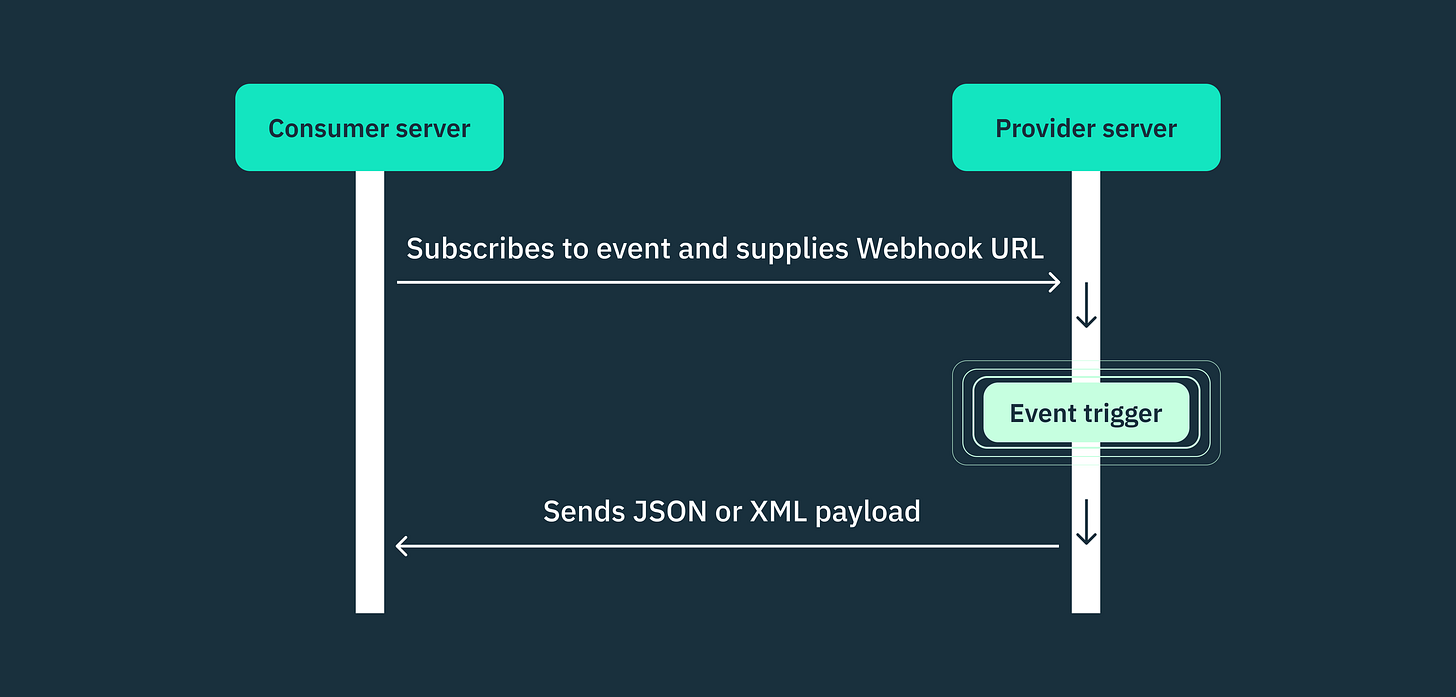
At its core, a webhook is a mechanism that allows one application to send real-time data to another application the exact moment a specific event occurs.
Instead of your application constantly asking a third-party service if there is new data, the third-party service simply pushes the data to your application as soon as it is available. This inversion of control makes webhooks incredibly fast and highly efficient, forming the backbone of the modern event-driven web.
1. The Core Concept: Polling vs. Webhooks
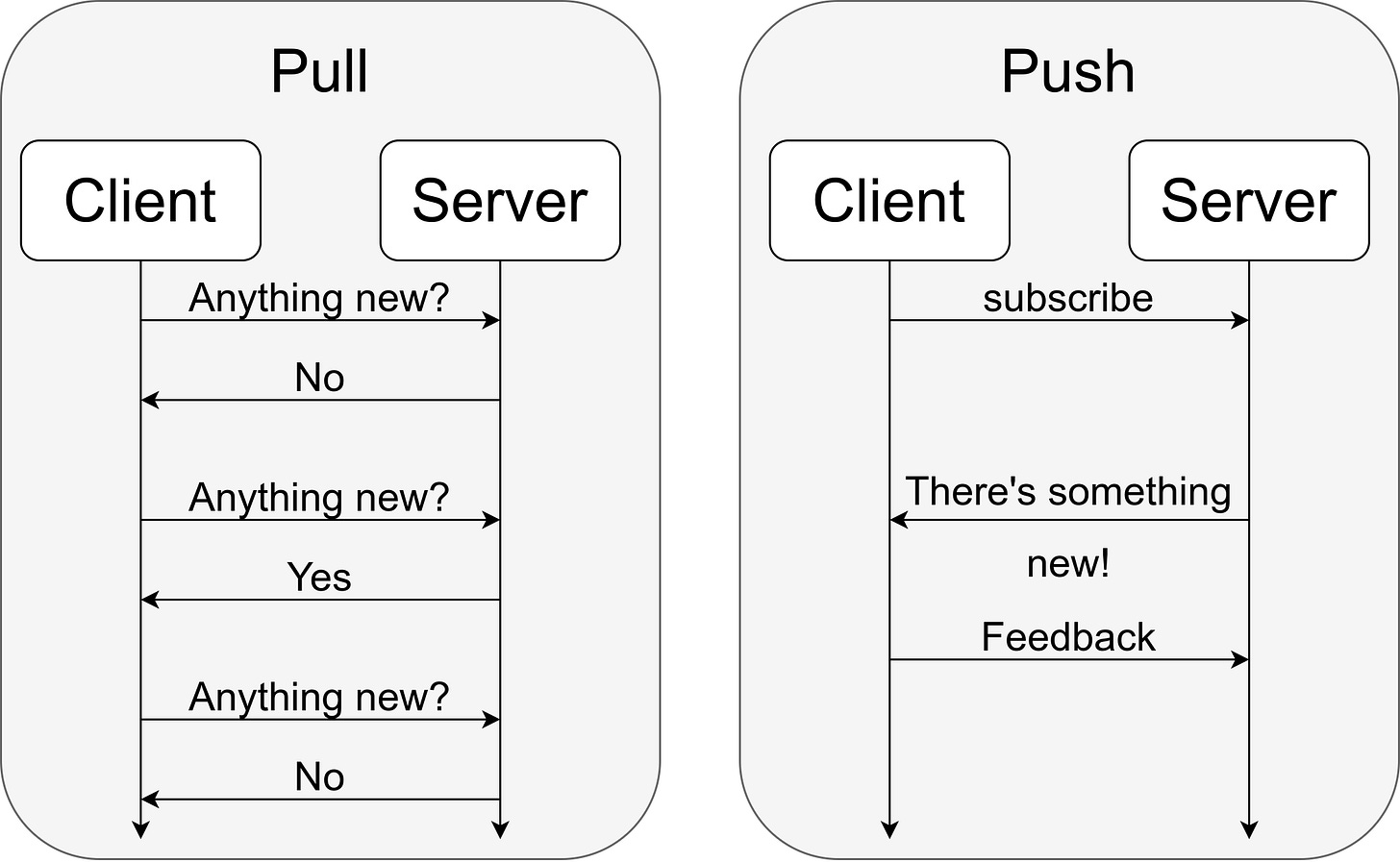
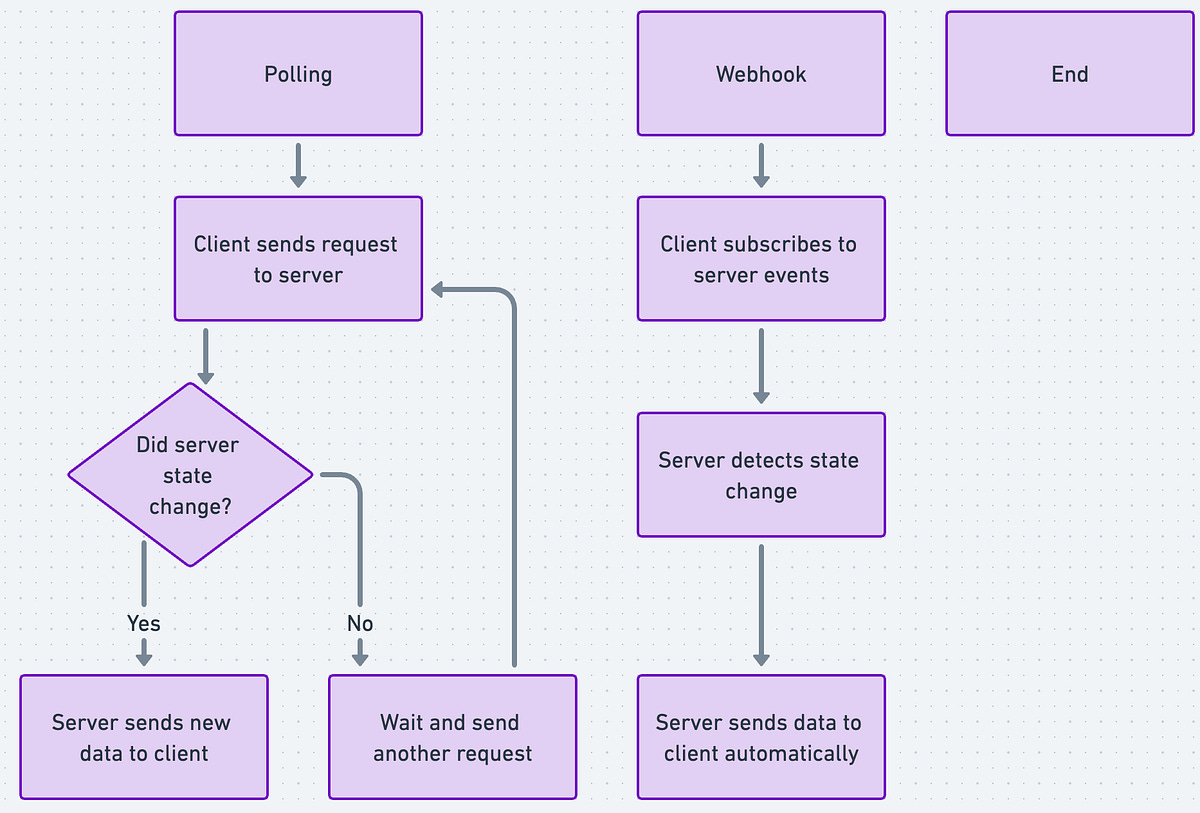
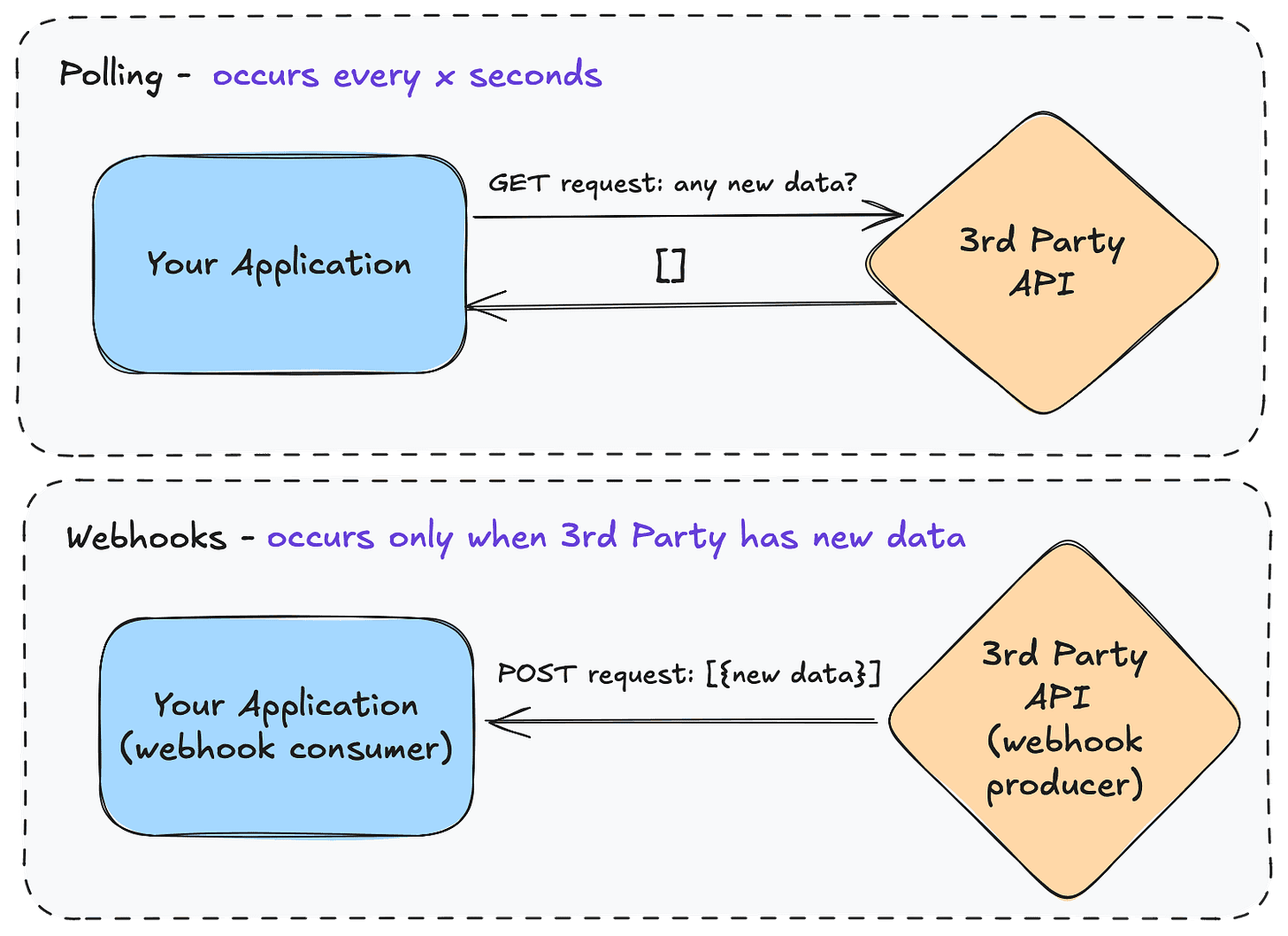
To understand why webhooks are a fundamental architectural requirement, you must understand the alternative: API Polling.
Imagine you order a physical product for delivery.
Polling (The legacy approach): You call the store every 5 minutes and ask, “Is my package ready?” Most of the time they say, “No.” You waste your time, and you consume the store’s resources. In software architecture, this means your server continuously sends HTTP
GETrequests to an external service just to check for state changes. It wastes massive amounts of CPU, memory, and network bandwidth for both systems.Webhooks (The event-driven approach): You give the store your phone number. You wait. When the package is ready, the delivery driver calls you. In software architecture, you provide the external service with a specific destination URL (your “phone number”). When an event happens, the external service executes an HTTP
POSTrequest containing the data directly to that URL.
Webhooks use a “push” model (server-to-client), while polling uses a “pull” model (client-to-server). Webhooks are event-driven, real-time HTTP callbacks, whereas polling involves periodic, scheduled requests to check for new data.
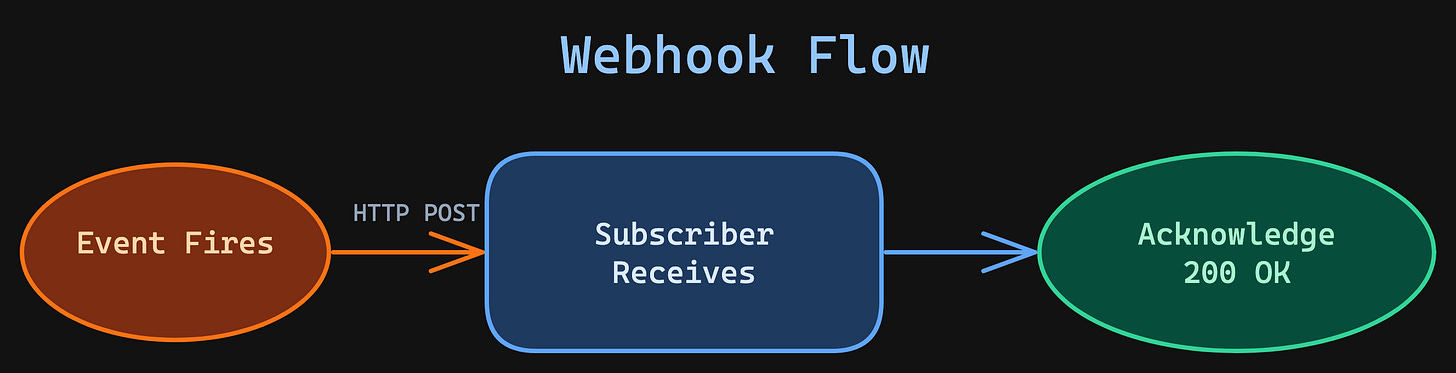
2. The Operational Flow
A standard webhook transaction follows a strict lifecycle:
The Trigger: An event occurs in the source system. For example, a customer successfully pays an invoice on Stripe, or a developer merges code on GitHub.
The Payload: The source system bundles all the relevant data about that event into a structured JSON object.
The Delivery: The source system sends an HTTP
POSTrequest containing that JSON payload to your pre-configured destination URL (e.g.,[https://api.your-app.com/webhooks/stripe](https://api.your-app.com/webhooks/stripe)).The Acknowledgment: Your server receives the payload, processes the data (like updating a user’s subscription tier in your database), and immediately responds with an HTTP
200 OKstatus code to inform the source system that the message was received successfully.
𝐋𝐞𝐚𝐫𝐧 𝐭𝐨 𝐛𝐮𝐢𝐥𝐝 𝐆𝐢𝐭, 𝐃𝐨𝐜𝐤𝐞𝐫, 𝐑𝐞𝐝𝐢𝐬, 𝐇𝐓𝐓𝐏 𝐬𝐞𝐫𝐯𝐞𝐫𝐬, 𝐚𝐧𝐝 𝐜𝐨𝐦𝐩𝐢𝐥𝐞𝐫𝐬, 𝐟𝐫𝐨𝐦 𝐬𝐜𝐫𝐚𝐭𝐜𝐡. Get 40% OFF CodeCrafters: https://app.codecrafters.io/join?via=the-coding-gopher
3. Moving to Production
The conceptual flow of a webhook is simple, but moving it into production requires assuming the internet is hostile and networks are unreliable. A production-grade webhook integration must solve three major architectural challenges: Security, Resiliency, and Idempotency.
Challenge A: The Anatomy of the Payload and Security
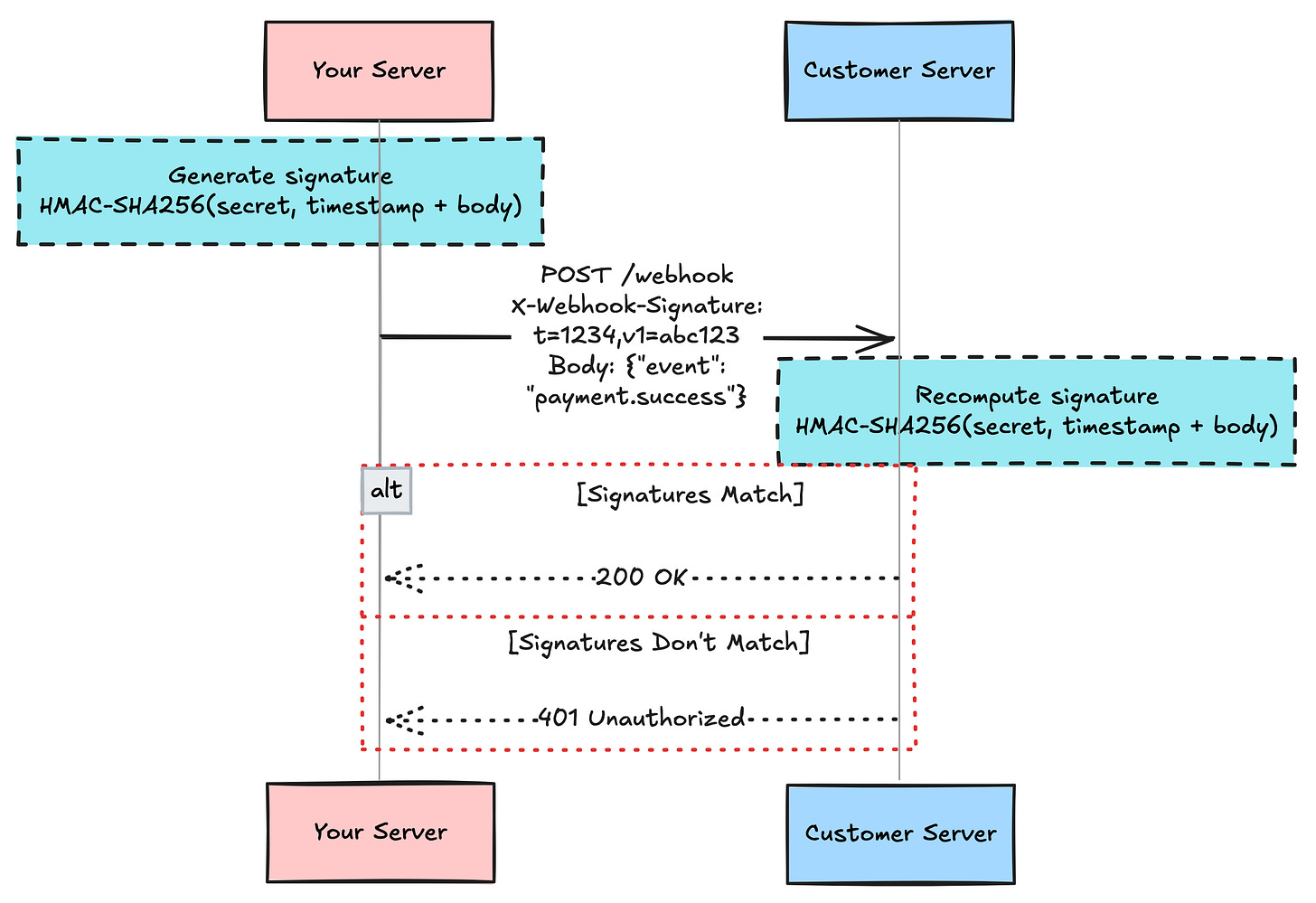
Because a webhook is simply an open, public-facing URL on the internet, it is inherently vulnerable. If you blindly accept incoming data, a malicious actor could send a fake POST request dictating that they successfully paid for a premium account.
Legitimate providers secure their webhooks using Cryptographic Signatures.
When you configure the webhook with a provider (like Stripe), they issue you a secret key.
When the provider dispatches a webhook, they use that secret key and a hashing algorithm (usually HMAC SHA-256) to generate a unique signature based on the payload’s contents. They attach this signature to the HTTP Headers of the request.
When your server receives the request, it extracts the raw JSON body and applies the exact same mathematical formula using your local copy of the secret key.
If your generated signature matches the header signature exactly, you have mathematical certainty that the payload originated from the trusted provider and was not tampered with in transit.
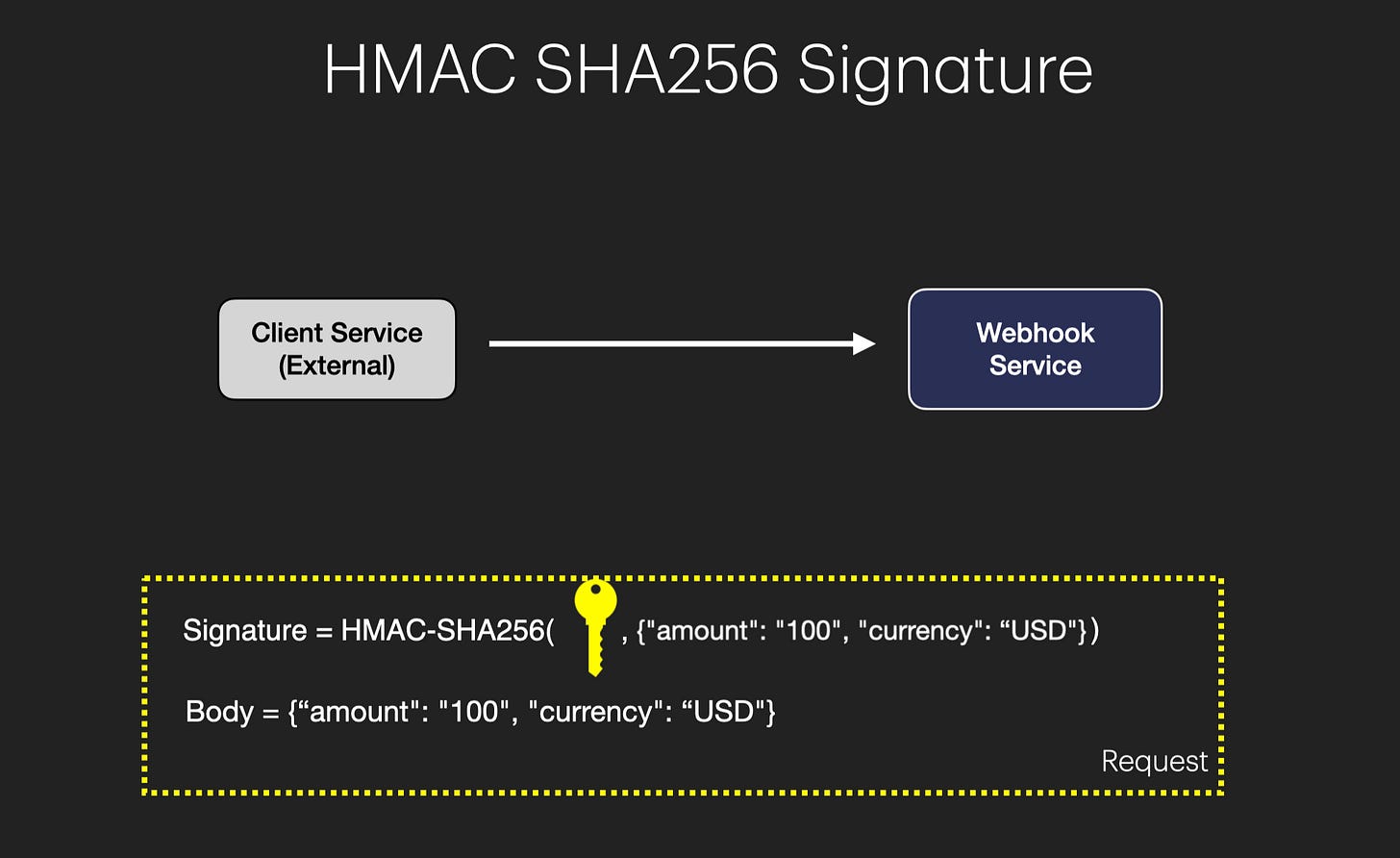
Note: While SHA-256 is a public, one-way hash function (used for checksums), HMAC-SHA256 requires a secret key to produce the hash, offering authentication in addition to integrity.
Challenge B: Resiliency and Handling Failures
Network cables get cut, databases lock up, and servers restart. If a webhook is dispatched while your server is temporarily offline, the request will fail. Because webhooks are asynchronous push events, the source system only knows you failed to receive it if you do not return a 200 OK status.
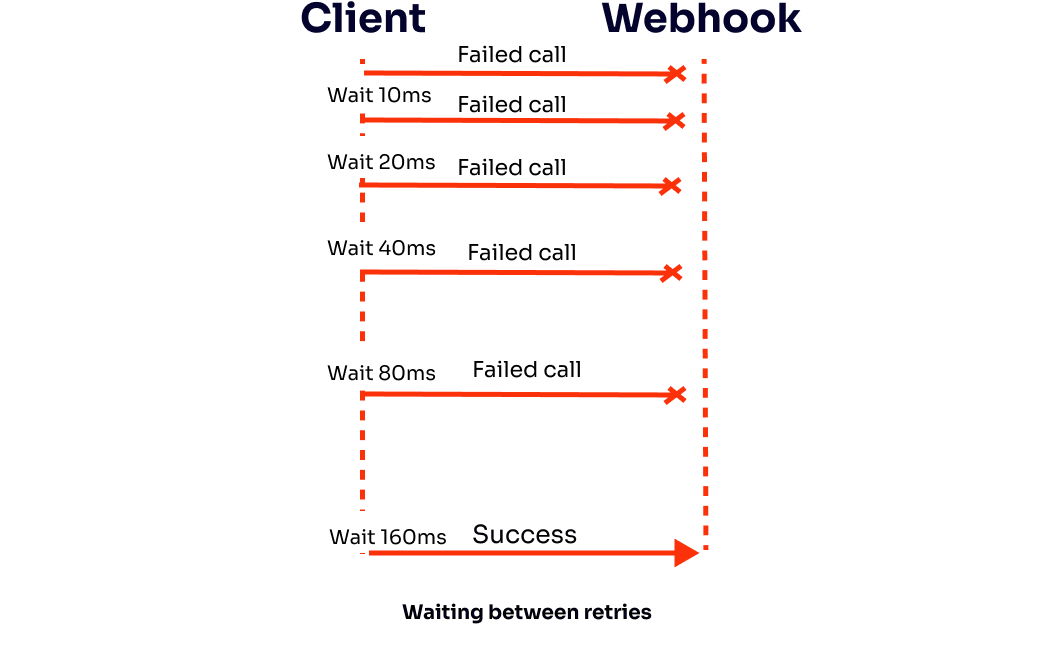
Robust providers implement an Exponential Backoff Retry Schedule. If your server returns a 500 Internal Server Error or times out, the provider will try again in 5 minutes, then 30 minutes, then 2 hours, up to several days.
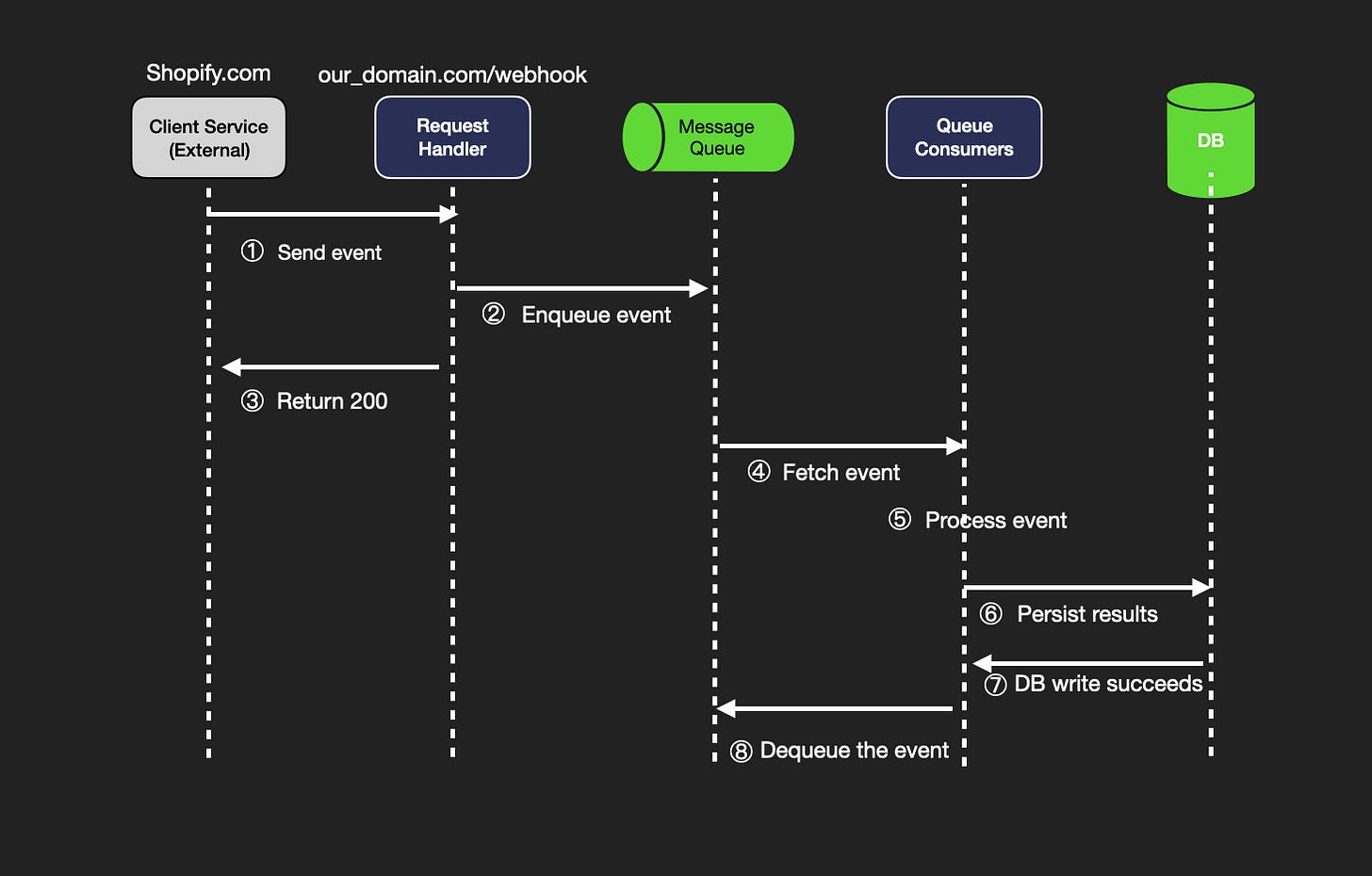
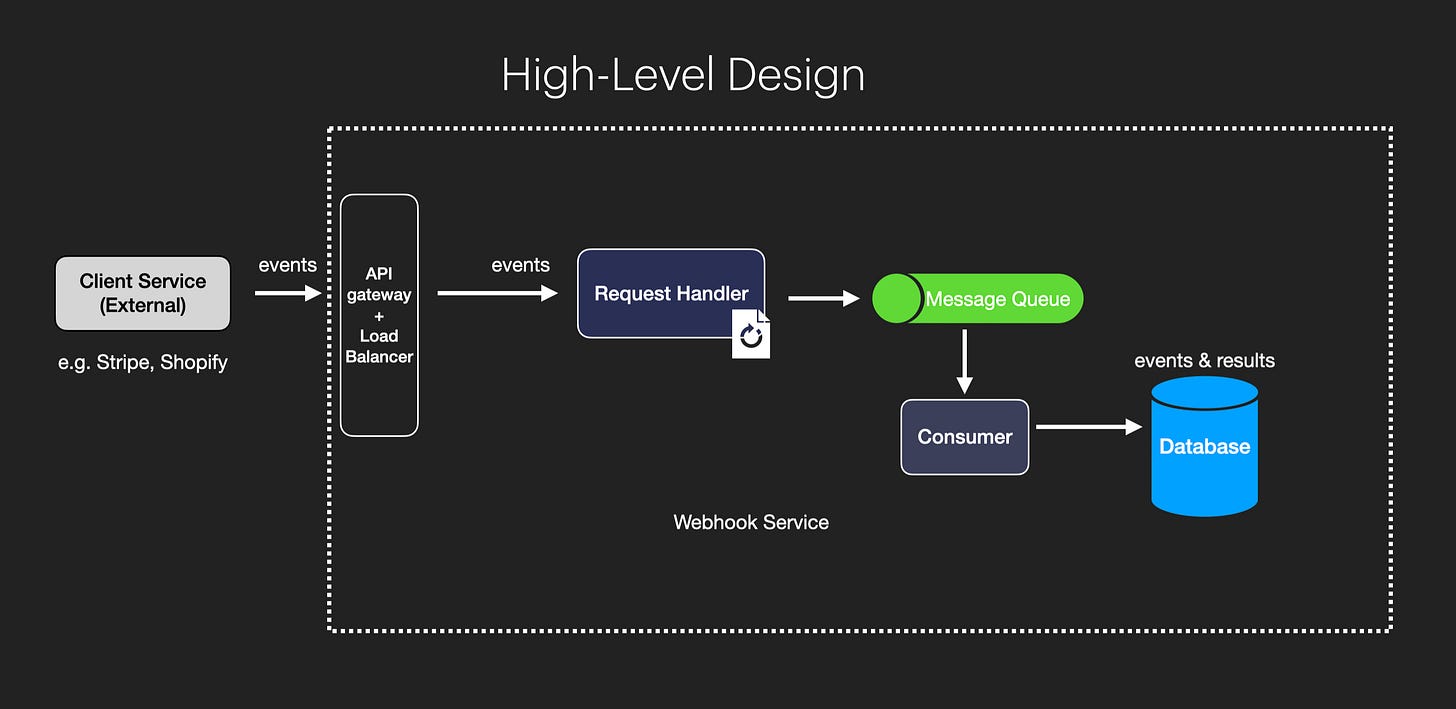
The Engineering Best Practice: Because providers expect a fast acknowledgment (typically within 3 seconds), your webhook endpoint should do as little synchronous compute as possible. The optimal architecture is to receive the payload, instantly push it into an asynchronous message queue (like Kafka, RabbitMQ, or AWS SQS), immediately return a 200 OK to the provider, and allow your background worker nodes to process the actual database updates at their own pace.
Challenge C: The Idempotency Problem
Network timeouts create a dangerous edge case: double delivery.
The provider sends the webhook.
Your server processes the data and upgrades the user’s account.
Your server attempts to send the
200 OKacknowledgment, but a network blip drops the packet.The provider assumes the delivery failed and sends the exact same webhook payload an hour later.
Your system must utilize Idempotent Processing. Idempotency dictates that an operation can be applied multiple times without altering the result beyond the initial application.
Every webhook payload contains a unique Event ID. Before your application executes any database mutations, it must query a persistent store: “Has this specific Event ID been processed before?” If the ID exists in your ledger, you safely ignore the duplicate payload and return a 200 OK to satisfy the provider.
4. Real-World Implementations
Webhooks are the connective tissue of modern third-party API integrations. Standard use cases include:
E-Commerce (Shopify/Stripe): When a payment clears, the payment gateway dispatches a webhook to your fulfillment server, automatically triggering the generation of a shipping label.
Continuous Integration (GitHub/GitLab): When an engineer merges a pull request into the
mainbranch, the repository dispatches a webhook to a CI/CD pipeline (like AWS CodeBuild or Vercel) to initiate automated testing and deployment.ChatOps (Slack/Discord): When monitoring software (like Datadog) detects a server CPU spike, it sends a webhook to your team’s Slack channel, instantly alerting the on-call engineers.