Understanding User Mode and Kernel Mode
Two Worlds Inside One CPU
“There is no security without separation. There is no stability without boundaries.” - Andrew S. Tanenbaum
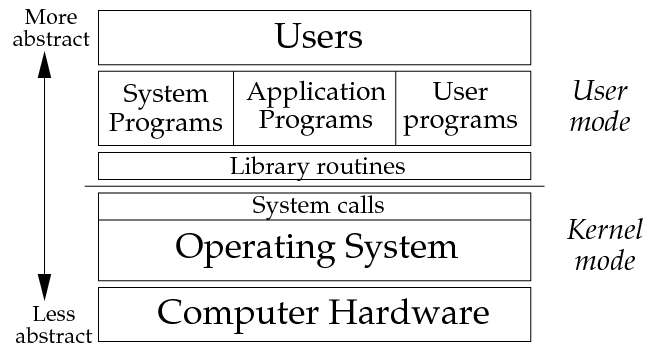
When we talk about performance or correctness in systems programming, one idea often gets thrown around casually: user mode versus kernel mode. It sounds simple, but like most things in systems, the details matter. Understanding what actually happens in each mode helps you predict latency, debug strange behavior, and write code that interacts with the operating system in a more intentional way.
The Core Idea of Dual Modes
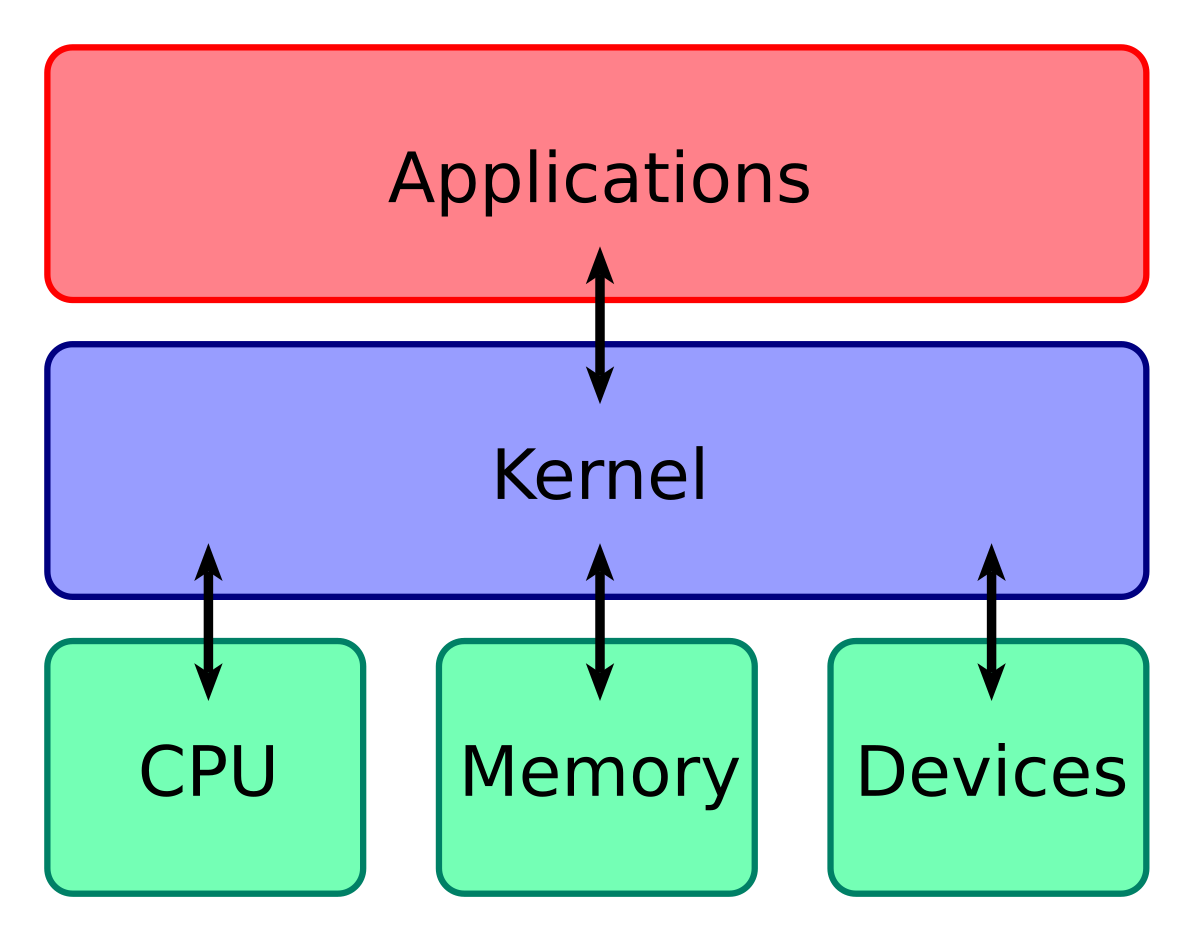
The modern CPU operates in at least two major privilege levels. User mode is the lower privilege level, where normal programs run. Kernel mode is the higher privilege level, where the operating system executes. Together these modes create a balance between freedom and safety. User mode programs can run arbitrary code supplied by anyone, but the CPU ensures they cannot modify hardware registers, program DMA controllers, reconfigure interrupt routing, or access memory that belongs to the kernel or another process. Kernel mode exists precisely because the OS must perform privileged operations that would crash or compromise the machine if untrusted code attempted them.
Life in User Mode
User mode is a curated environment. Your process lives inside a private virtual address space* constructed and maintained by the operating system. Everything you think of as memory—your stack, your heap, your code—is mapped into this synthetic space. You are free to read and write within its boundaries, but any attempt to read illegal memory or write to regions marked read-only will cause the CPU to trap into the kernel. At that point, the OS decides whether the violation is resolvable, such as loading in a missing page from disk, or whether the process must be terminated. User mode therefore feels flexible, but it is a controlled illusion designed to keep programs isolated and safe.
* A virtual address space is the isolated range of memory addresses an operating system gives to each process, creating a private, large, and consistent view of memory, separate from physical RAM. It uses virtual-to-physical address translation (via page tables) to map these virtual addresses to actual physical RAM locations or even disk storage (paging).
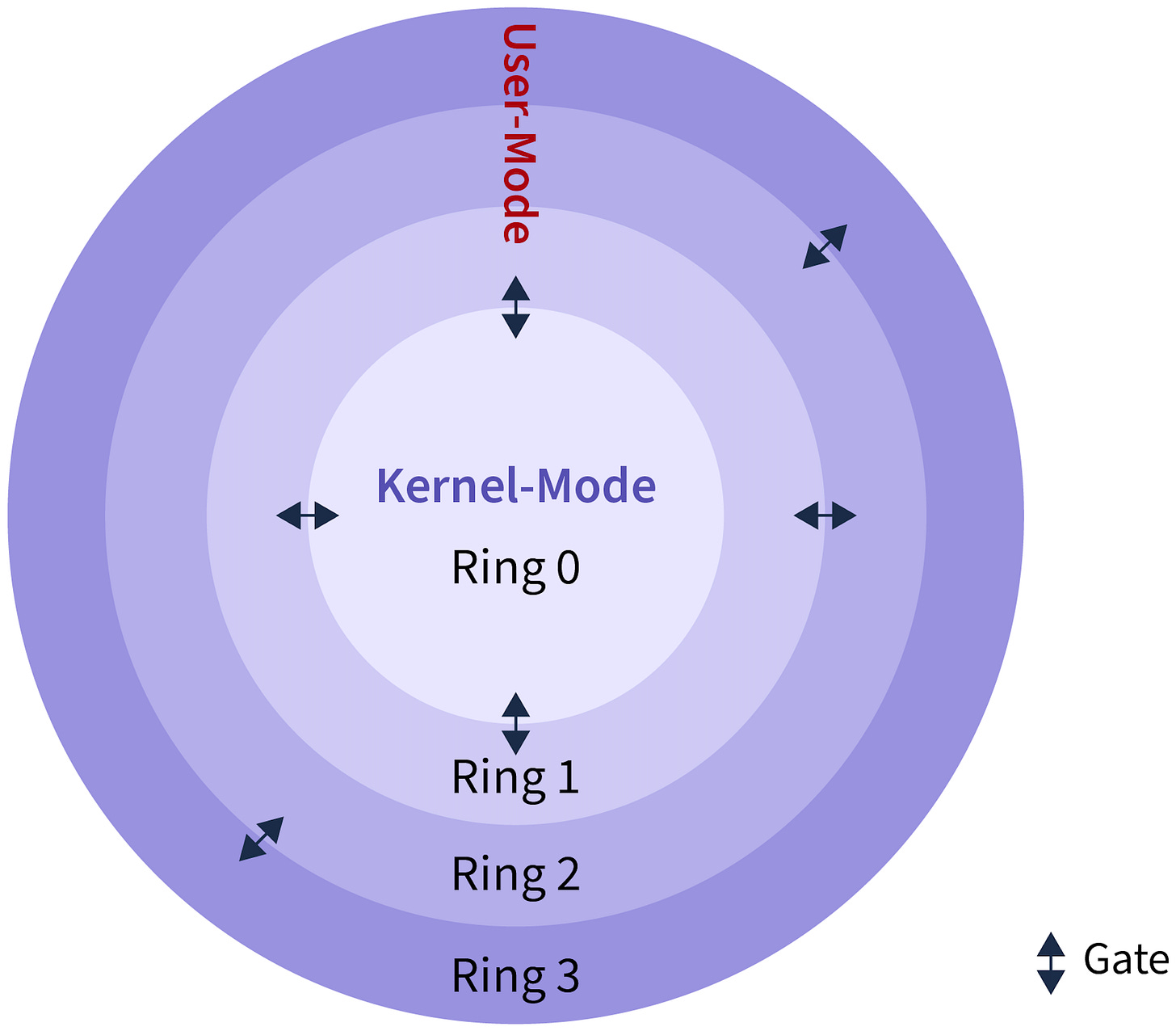
User mode (Ring 3) runs applications with restricted access, while Kernel mode (Ring 0) is the highly privileged core of the OS, with full hardware access, using CPU protection rings (like Ring 0 for Kernel, Ring 3 for User) to enforce security, ensuring user apps must use system calls (APIs) to interact with hardware, preventing a single app crash from bringing down the whole system. Rings 1 and 2 are rarely used but offer intermediate privilege, creating a hierarchy for resource management and stability.
User Mode (Ring 3)
Privilege. Least privileged, restricted.
What Runs. User applications (browsers, games, text editors).
Access. Cannot directly access hardware or kernel memory; uses system calls (APIs) to request services from the kernel.
Isolation. Each process has its own memory space, so a crash only affects that application, not the entire system.
Kernel Mode (Ring 0)
Privilege. Most privileged, unrestricted.
What Runs. The operating system kernel and trusted device drivers.
Access. Full, direct access to all hardware (CPU, memory, I/O) and all system resources.
Impact. Errors here are severe and can crash the entire operating system.
Protection Rings
A hardware-enforced security feature.
Ring 0. Kernel Mode (highest privilege).
Ring 1 & 2. Rarely used in general OS, sometimes for drivers/virtualization.
Ring 3. User Mode (lowest privilege).
Mechanism. CPU hardware prevents code in a lower ring (like Ring 3) from executing privileged instructions or accessing memory outside its bounds, causing an exception (trappable error).
The Power and Peril of Kernel Mode
Kernel Mode is a hardware-enforced state (typically Ring 0 on x86 or EL1 on ARM) that grants the CPU permission to execute privileged instructions. While User Mode applications are restricted to safe operations, Kernel Mode can execute instructions that control the machine itself, such as halting the processor, disabling interrupts, or accessing physical hardware ports.
Because the kernel manages the hardware, it operates without the safety nets provided to standard applications.
The “Watcher” Problem. In User Mode, if a program tries to access forbidden memory, the hardware (MMU) catches it and notifies the OS to kill the process (Segmentation Fault). However, the Kernel configures the MMU. If the Kernel writes to the wrong address, there is no higher-level supervisor to stop it. It can accidentally overwrite the Page Tables—the very maps the CPU uses to locate memory—causing the system to lose track of where data exists.
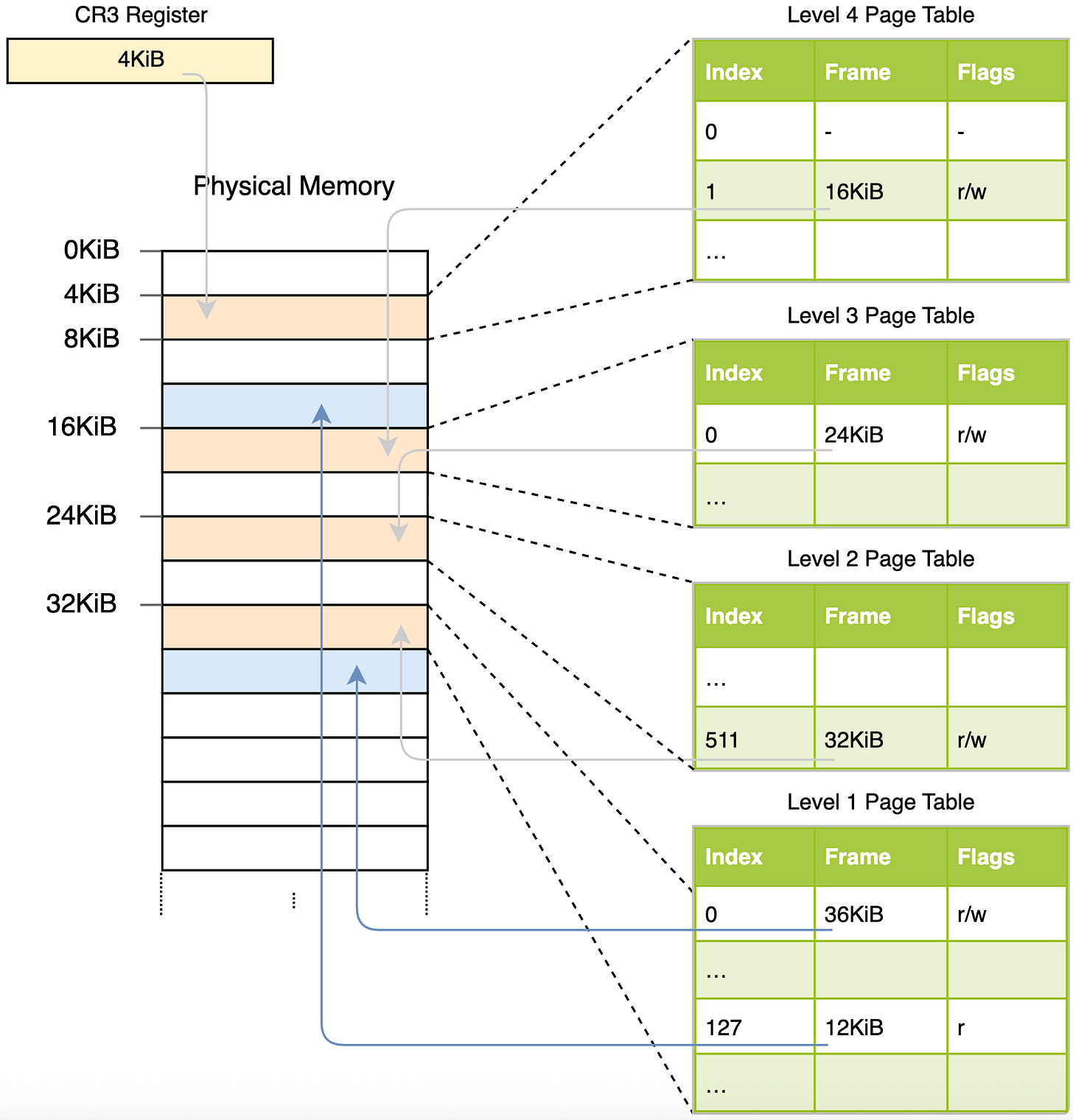
One set of page table for use in kernel mode includes both kernel-space and user-space. The second set of page table for use in user mode contains a copy of user-space and a minimal set of kernel-space handling system calls and interrupts.
The above describes the architecture of Kernel Page Table Isolation (KPTI), a security feature (like in Linux) that splits memory into separate user/kernel page tables to prevent Meltdown-type attacks by isolating kernel data from user processes, even when switching contexts, ensuring user mode can’t read privileged kernel info, only the minimal necessary mappings for system calls. One full table (kernel mode) maps everything; a second, restricted table (user mode) maps user space plus a small, safe kernel stub for exceptions/syscalls, stopping speculative execution from snooping.
The CR3 Register is a specialized hardware register in the CPU that acts as the “root pointer” for the current process’s memory map.
The Directory Pointer. It holds the physical address of the top-level Page Table. This tells the CPU where to begin translating virtual addresses (what code uses) into physical RAM addresses (where data lives).
The Context Switch. When the OS switches from Process A to Process B, it simply updates the CR3 register.
The Result. Instantly, the CPU is pointing to a completely different set of Page Tables. The entire view of memory changes, ensuring Process B cannot see or touch Process A’s data.
In short. Changing the value in CR3 is how the OS swaps the “world” the CPU sees.
The Power. By changing the value in CR3, the kernel performs a Context Switch, instantly swapping the entire “universe” of memory. One moment, virtual address
0x4000points to your web browser’s data; the next moment, it points to a text editor’s code.The Risk. Since the kernel can write to the physical memory that holds these tables, a bug here is catastrophic. If the kernel corrupts the Active Page Directory, it doesn’t just crash a program—it corrupts the CPU’s ability to interpret any address, essentially blinding the processor.
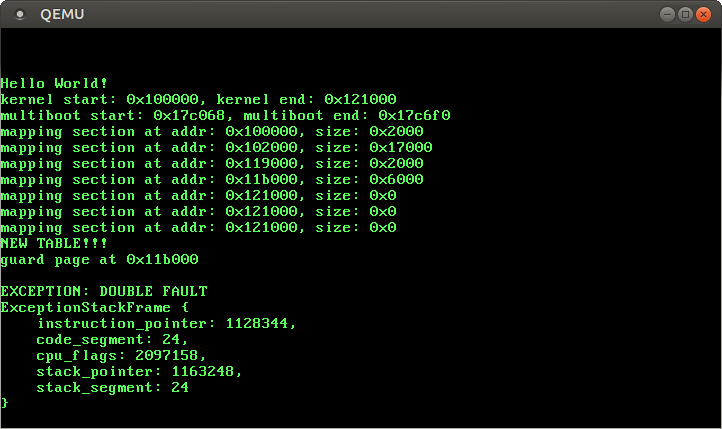
The Triple Fault. Error handling relies on the IDT (Interrupt Descriptor Table). If the kernel triggers a fault (like a null pointer dereference), the CPU tries to run the registered error handler. If that handler also fails (a Double Fault), and the Double Fault handler fails, the CPU has no software left to execute. It triggers a Triple Fault and instantly hard-resets the physical machine.
This is why kernel development requires extreme discipline: you are not writing code that runs on the computer; you are writing the code that defines the computer for everyone else.
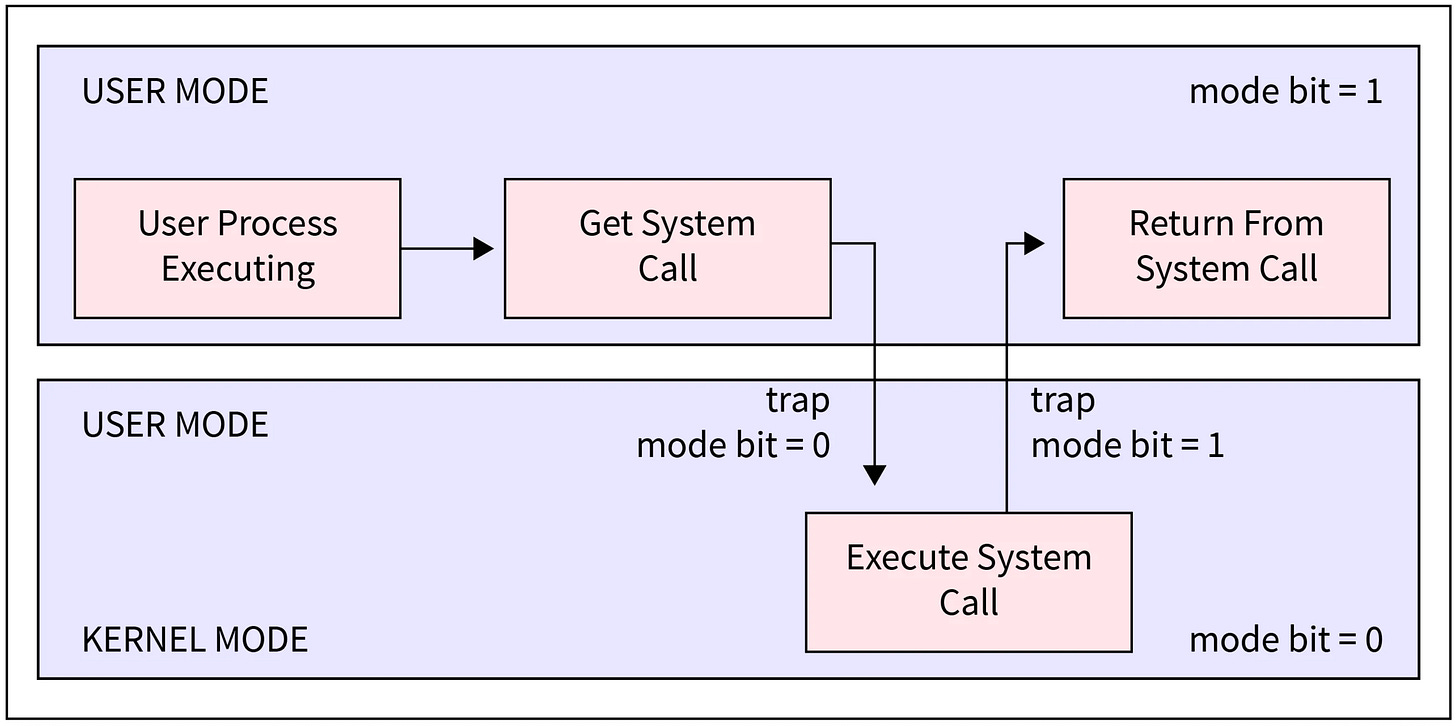
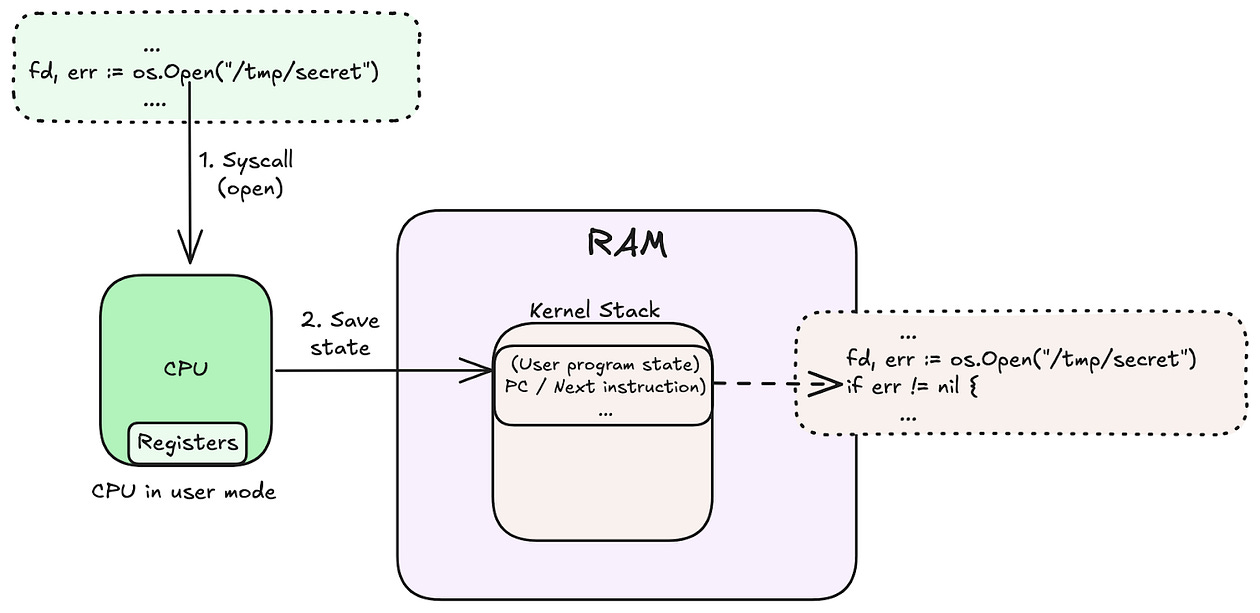
Crossing the Boundary with System Calls
A system call is not a function call; it is a request for a hardware-level intervention. When your program needs a privileged operation (like reading a file or sending network packets), it cannot just “jump” to kernel code.
The Trigger. The program executes a special instruction (like
SYSCALL) that deliberately triggers a hardware trap.The Switch. The CPU catches this trap, immediately elevates privilege levels (Ring 3 to Ring 0), and switches to a secure Kernel Stack.
The Execution. The CPU jumps to a predefined handler in the kernel to perform the work.
The Return. Once finished, the kernel uses a special instruction (like
SYSRET) to drop privileges back to User Mode and resume your program exactly where it left off.
This entire round-trip happens millions of times per second, serving as the secure bridge between your code and the hardware.
The Hidden Cost of Switching Modes
A system call (syscall) is not just a function call; it is a request for the operating system to take over. This requires the CPU to stop running your code, switch modes, and jump into the kernel.
This process introduces overhead in three distinct phases: the Mode Switch, the Hardware Disruption, and the potential Context Switch.
1. The Mode Switch (Crossing the Border)
The CPU cannot simply jump from user code to kernel code. It must perform a secure transition from “User Mode” (low privilege) to “Kernel Mode” (high privilege). This involves several mandatory steps:
Trap Instruction. The CPU executes a special instruction (like
SYSCALLon x86) that triggers a hardware exception to pause the current process.Saving State. The CPU must save the current state of your program (registers, instruction pointer, stack pointer) so it can resume exactly where it left off later.
Loading Kernel State. The CPU loads the kernel’s stack and execution context to begin processing the request.
2. Hardware Disruption (The Cache Penalty)
The biggest performance hit often comes after the switch. Modern CPUs rely heavily on caches (L1/L2/L3) and the TLB (Translation Lookaside Buffer) to run fast. System calls disrupt this efficiency.
TLB Pollution. The kernel uses different memory addresses than your program. Accessing kernel memory can evict your program’s entries from the TLB, leading to slower memory access when your program resumes.
Cache Trashing. The kernel code and data will be loaded into the CPU caches, potentially overwriting the “hot” data your program was using. When control returns to you, your data has to be fetched from slow RAM again.
3. The Scheduling Risk (The Context Switch)
A simple system call might return immediately, but it also gives the OS a chance to run the scheduler.
Involuntary Pause. If the OS decides your “time slice” is up, or if the syscall requires waiting for I/O (like reading a file), the kernel will put your process to sleep.
Full Context Switch. The OS will then load a completely different thread or process. This is the most expensive scenario, as it compounds all the costs above—invalidating virtually all caches and TLB entries relevant to your code.
Interrupts, Exceptions, and Involuntary Mode Changes
While system calls are voluntary, interrupts are not. When hardware needs attention—network packets arriving, timers firing, storage completing reads—it forces the CPU into kernel mode to run the appropriate interrupt handler. Exceptions such as divide-by-zero, page faults, or invalid memory accesses also route code into the kernel. The OS must decide whether the event can be resolved or whether the process must be terminated. These involuntary transitions make it clear why kernel stability is paramount: the entire system depends on the correctness of the kernel’s reactions to unexpected events.
Scheduling and the Role of Kernel Mode
Every thread begins in user mode, but scheduling decisions happen exclusively in kernel mode. When a thread blocks on I/O, yields, or exhausts its time slice, the kernel intervenes. It captures the thread’s state, updates scheduling queues, and restores another thread’s context. The ability of the kernel to preempt user mode execution ensures fairness and responsiveness. Without this mechanism, a single misbehaving program could monopolize the CPU indefinitely.
Why This Boundary Matters
Once you understand the line between user mode and kernel mode, the behavior of your programs becomes far easier to interpret. A stalled system call means the kernel is waiting on a resource. A segmentation fault means the CPU trapped into the kernel after detecting an illegal memory access. A sudden increase in latency may mean more time is being spent inside kernel operations or more context switches are occurring. High level languages and frameworks rely on these mechanics at every turn, even if they never mention them explicitly.
Grasping this dual mode architecture gives you a more truthful mental model of how software and hardware cooperate. Every action your program performs, from opening a file to spawning a thread to touching virtual memory, is part of a negotiation between the unprivileged world and the privileged one. The clearer that negotiation becomes, the more precisely you can write and optimize software that lives in it.



appreciate all the drops!!! excited to read them all